It’s the week before holiday break. No doubt there’s plenty on your plate. Kids free from school, last-minute work projects, trying to guess what your teenage niece wants for Christmas. Cybersecurity threats should be last on that list.
But every year, we see an alarming pattern.
Businesses go on skeleton crew and cybersecurity threats strike. No one’s in the office, no one’s at home to help, no choice but to call an expensive Hail Mary. It’s an annual reality for too many companies.
So the big question this time of year is: Who’s handling your IT when everyone’s gone?
Quick Navigation
Statistics on Holiday Cybersecurity Threats
Let’s go through some eye-opening facts:
- DDoS attacks are highest at this time of year
- DDoS attacks almost doubled in Q4 2019 compared to 2018
- 28% of attacks happen on the weekend
- Majority of cybersecurity threats are malware, social engineering, hacking and DDoS attacks
- In 2019, phishing emails were the biggest threat for schools, healthcare businesses and government entities
- Commonly targeted industries in Q4 are healthcare, finance and government
Sources: Curotec, BitNinja, Deccan Chronicle, iVenture
Defined For You: What is DDoS – Distributed Denial-of-Service and other threats?
These charts present a detailed picture of December 2019’s cybercrime landscape. We can assume 2020 will follow a similar pattern.
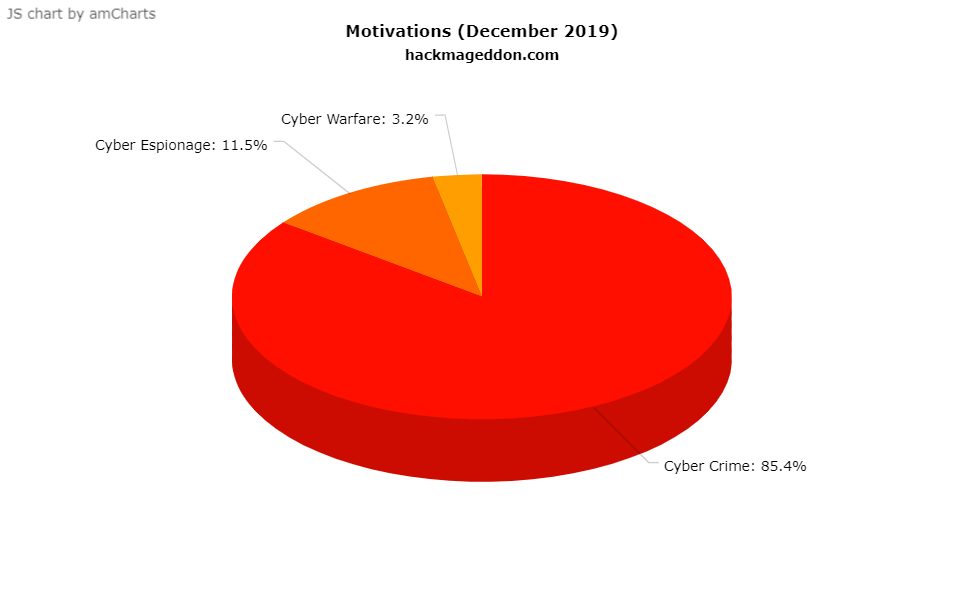
As you can see, the majority of malicious intent is based on actual crime. Hackers are done spying, they’re acting out on knowledge gathered from weeks and months past.
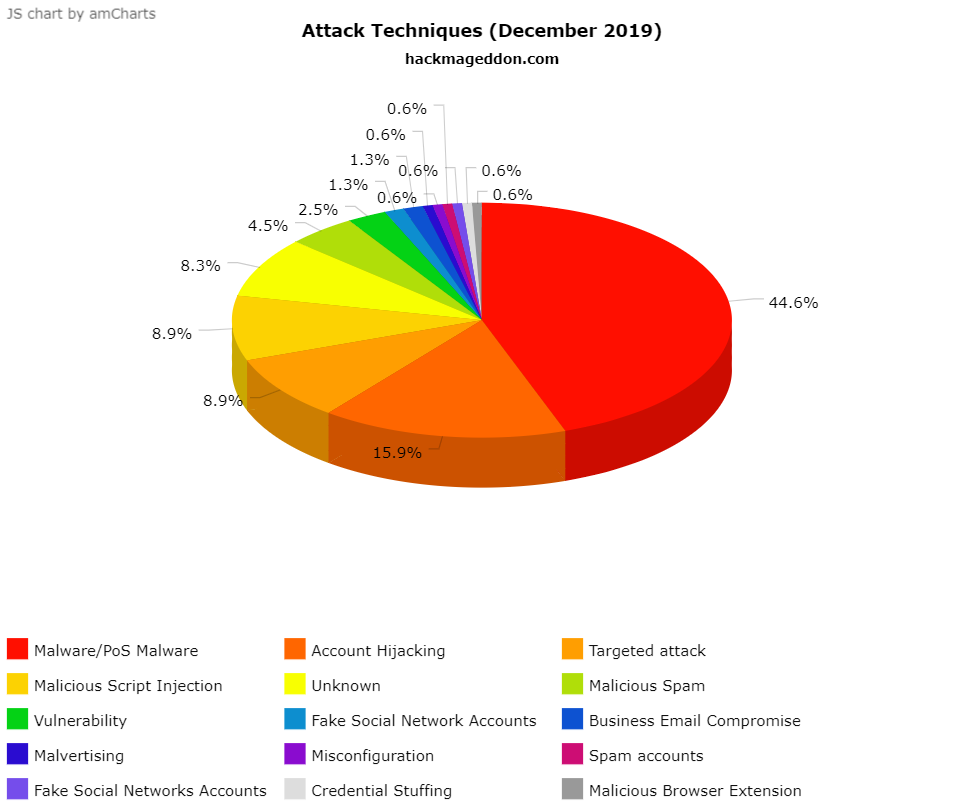
This chart shows the incredible amount of ways hackers commit crime. In Q4 of 2019, malware was the most common technique, followed by hijacking, then targeted attacks and SQL injections.
Defined For You: SQL injections, drive-by downloads and more weird cybersecurity threats
The Answer To Holiday Cybersecurity Threats
Don’t sacrifice your well-deserved holiday time to hackers. There’s a way to monitor and manage cybersecurity without being on-call on Christmas day. Cover all bases with a managed service provider (MSP).
What is a Managed Service Provider?
A managed service provider (MSP) provides end-to-end IT and security services. With an MSP, your entire IT environment is handled from one trusted resource.
MSPs fill four important roles that businesses need. Resource, Guide, Facilitator and Guardian. This shield sums up the roles and responsibilities nicely.

MSPs are the reinforcement to business security. Just be sure it’s an A+ MSP, not those other guys. That means:
- 24/7/365 support
- True fixed-fee plans
- Predictable IT spend
- Unlimited onsite and remote support
- No surprise “Big Project” bills
- Dedicated team structures
- Full transparency and reporting
Learn About IT Plans Fit For You
All-Inclusive IT Services: give your business the benefits of a full IT department without worrying about building and managing your own. It’s ideal for businesses without internal IT or IT executives looking to refocus their internal IT team. Learn more.
Supplemental IT services: give your IT department more bandwidth and access to specialty expertise. It’s ideal for businesses who want to get more out of their existing IT team. Learn more.
Let’s get real. December isn’t the only month for cybersecurity. Companies need defense year-long. So make this a Christmas gift or a New Year’s wish come true for your business. Let’s talk about your goals today.
Contact our team today. iVenture’s award-winning team delivers managed services, cloud and cybersecurity to Florida’s best businesses. With statewide coverage, our offices in Jacksonville, Orlando and Tampa make us your local IT partner. Whether you need end-to-end IT or a boost to your internal IT team, we’re ready. At iVenture, we give you more time to do what matters most.






